Device Manufacturers may have limited visibility of software components and their origin. An automated assessment process is required to provide SBOM manifest and security assurance into customer supply chains, for government procurement, and to meet major market regulatory requirements including the EU Cyber Resilience Act (CRA).
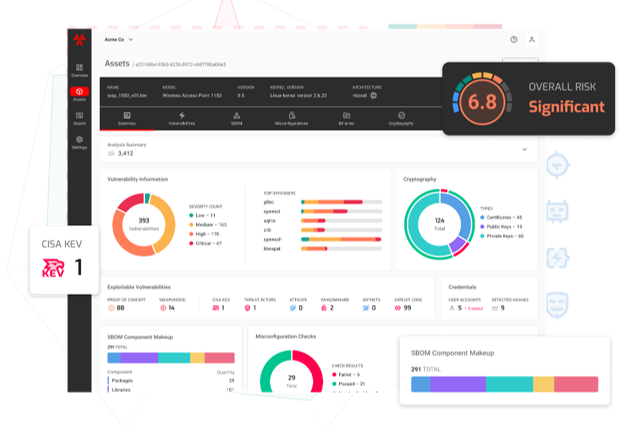
The Cypherbridge ESAS SaaS dashboard puts the control at your fingertips. Analyze compiled binaries, firmware, and software to detect vulnerabilities and security risks without requiring source code. Assess and continuously monitor edge device for precise detection of risks. Flag vulnerabilities and rank by priority. Around the clock, ESAS correlates the analyzed components against multiple databases for near-real-time risk assessment, including NVD, CISA KEV, and open source repositories. ESAS helps security teams focus on real threats, reduce response time, and lower operational costs.
Software Lifecycle: From Report to Repair
ESAS threat intelligence drives mitigation. The Cypherbridge CDX Device Management System closes the loop with comprehensive software lifecycle management, JIT device onboarding, event notification, telemetry and configuration, and Over the Air (OTA) software update for vulnerability patch and product feature upgrades.
ESAS Features
- Automated Assessment and Risk Analysis
- Binary software images scanned for CVEs, CWEs, embedded credentials
- Actionable and Timely Intelligence
- Continuous Monitoring and Real-Time Alert Reports
- Email notifications
- Integrated with support ticket tracking and reporting systems including Zendesk
- Software Bill of Materials SBOM
- Regulatory Compliance
- Support Chain Assurance
- Product Resiliency
- Mitigation and Remediation Engineering Services
Mitigate Security Vulnerabilities
Upgrade and modernize your IoT device fleet with the Cypherbridge SDKPac product family, including X.509 credentials management system across all related protocols including TLS, VPN, EAP-TLS, and uLoadXL secure boot code sign and verify. The SDKPac Credentials Manager provides the in-device trust store to manage built-in and dynamically provisioned credentials for CA, server and device certificates and private key pairs. Using the EST client, production systems can deploy managed credential services at scale. The EST client integrates as the device level and support credential management at each stage of the IoT device lifecycle including pilot and production, manufacturing line provisioning, device on-boarding, and long-term credential management